Hi, I'm Tao .
I write about
backend
,
cloud infra , and life .
Backend engineer working with Java, Rust, and the Cloudflare developer platform. Tutorials, field notes, and the occasional rant — usually written for my future self.
Last updated May 2026 · view archive
/ now
a snapshotCloudflare Workers + D1
Designing Data-Intensive Apps
Rust async runtimes
/ featured
All posts →
An Introduction to 3D Printing Technology: A Practical Guide to Terminology, Processes, and Development Pathways
A practical introduction to 3D printing technology, covering core terminology, common additive manufacturing processes, materials, software workflows, and learning paths for product managers, engineers, designers, makers, and beginners.
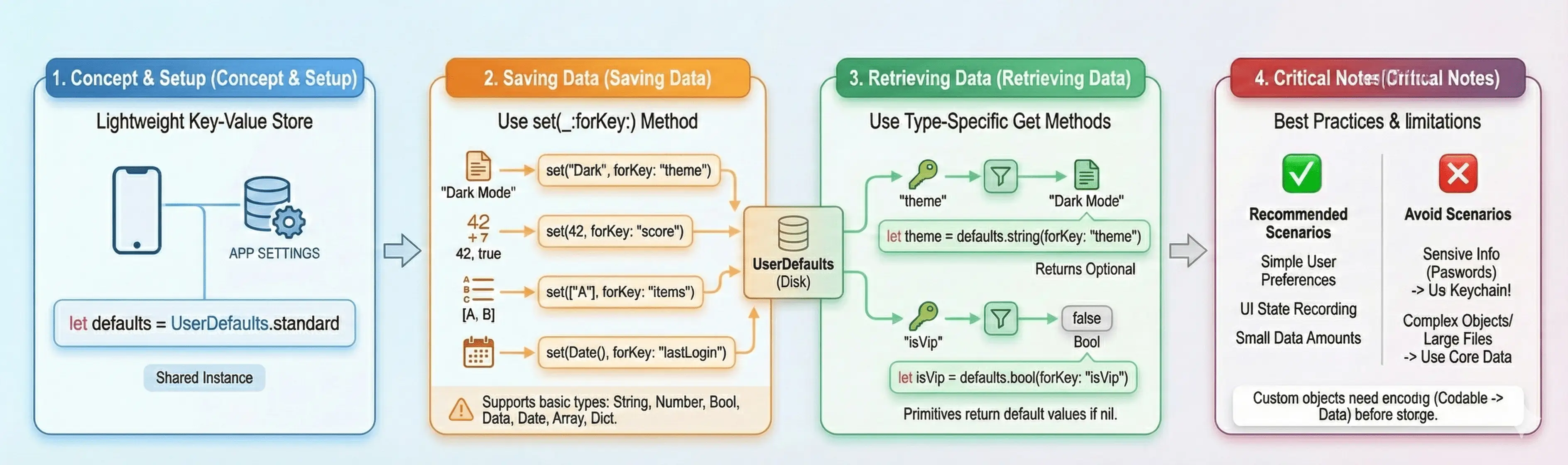
Complete Guide to Swift UserDefaults: From Basics to Advanced Practices
Deep dive into UserDefaults in Swift, learn how to store user preferences, handle custom objects, understand security best practices, and master the @AppStorage property wrapper in SwiftUI.
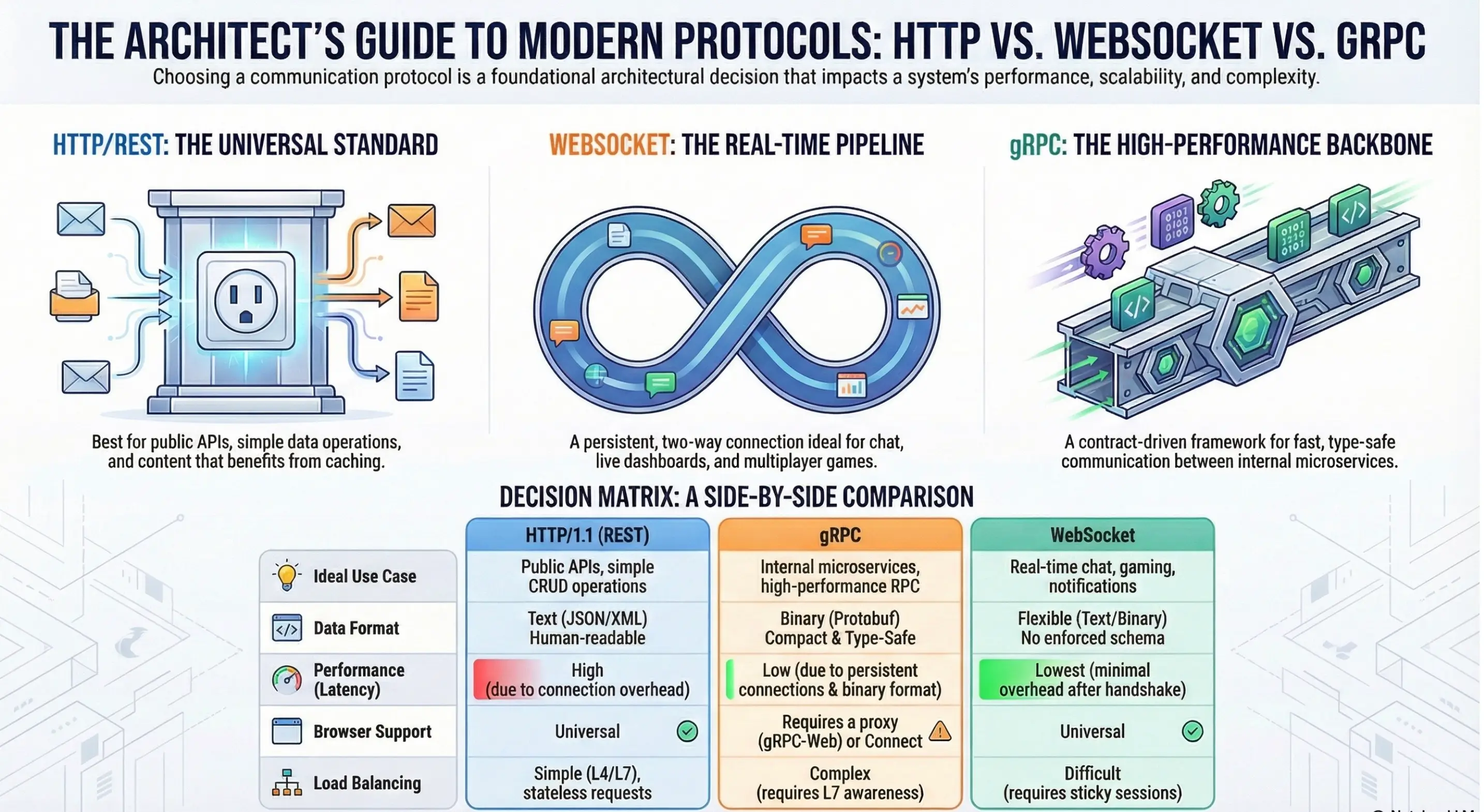
The Three Pillars of Modern Distributed Communication: An Architectural Analysis of HTTP, WebSocket, and gRPC
A systematic comparison of HTTP, WebSocket, and gRPC across transport mechanics, performance characteristics, browser support, operational complexity, and security models, providing an actionable decision framework for protocol selection in modern distributed systems and microservice architectures.
Podman Quadlet: A Simpler Way to Run Containers with systemd
A comprehensive guide to Podman Quadlet, learning how to manage container services using simple text files, implementing declarative container management, and replacing the traditional podman generate systemd method.

Building Your First Stateful Serverless Application with Cloudflare Durable Objects from Scratch
Comprehensive tutorial: Learn Cloudflare Durable Objects from scratch, build stateful serverless applications, implement globally distributed real-time counters, master the core concepts of stateful serverless development
Complete Guide: Deploying Payload CMS to Cloudflare Workers
Step-by-step tutorial on deploying powerful Payload CMS to Cloudflare Workers platform, integrating D1 database and R2 storage to build a globally distributed headless CMS
/ recent posts
Archive →- Dec 1 Complete Guide to Swift UserDefaults: From Basics to Advanced Practices →
- Nov 30 The Three Pillars of Modern Distributed Communication: An Architectural Analysis of HTTP, WebSocket, and gRPC →
- Nov 1 Podman Quadlet: A Simpler Way to Run Containers with systemd →
- Oct 16 Building Your First Stateful Serverless Application with Cloudflare Durable Objects from Scratch →
- Oct 6 Complete Guide: Deploying Payload CMS to Cloudflare Workers →
- Sep 14 Cloudflare Email Workers: Making Email Processing Smart →
- Aug 30 AdsPower for Facebook Multi-Account Management: A Complete Guide →
- Aug 15 The Complete Cloudflare Wrangler Guide: From Local Development to Global Deployment →
- Aug 10 Complete Guide to Securing SSH Access with Cloudflare Zero Trust →
- Aug 8 Understanding Podman Build: A Technical Deep Dive →
- Aug 2 Mastering podman run: Your Complete Guide to Modern Container Management →
/ topics
All →New posts. No spam. Pinky promise.
Subscribe via RSS, or just bookmark this page. I publish a few times a month.